What data does Signal store about me?
The short answer
The short answer is: not much.
Over time, Signal has received a few requests for data on their users from law enforcement. You can see their published list here. Their most recent one came from the FBI in October.
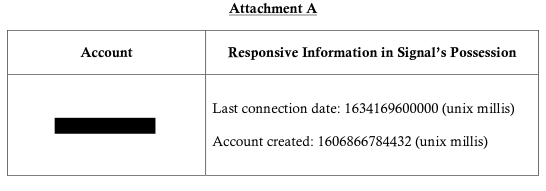
According to Signal’s response to the subpoena, when given the account (which is most likely a phone number), they were only able to provide the timestamp of when the account was created and the timestamp of the last time that account connected. It appears that this is the only data that they store about their users.
Contrast that to how much information the FBI requested in the subpoena. This is the information that the FBI requested about this particular user:
- Subscriber Information: Signal Messenger username/accounts with associated subscriber information to include if available: Full legal name, date and time of account creation, date of birth, photographs, phone number, home address, email, tax ID number, utility bills, and information from submitted photo ID (which may include passport number, driver’s license details, national identity card details, gender, or signature) if available
- Financial Information: Including bank account information, payment card primary account number (PAN), or other information about added payment methods if available
- Transaction History: Including information specific to financial transactions entered using Signal Messenger if available
- Job-Related Information: Including job title and any other provided descriptions of employment if available
- Online Behaviors: Including device data, site interactions, and cookies if available
- Activity Log: Including logs of click-stream data if available
- Communications: Including records of correspondence with Support team and subscriber information (listed above) of other users of Signal Messenger with dates/times that have communicated with the above referenced party or phone number if available
- Survey Responses: Including responses to any surveys completed for Signal Messenger LLC if available
- Connected Applications: Including applications connected through Signal Messenger account if available
- Referrals: Including information related to any referrals made to Signal Messenger LLC if available.
That’s potentially a lot of information! Additionally, there was this note:
- Please do not disclose/notify the user of the issuance of this subpoena. Disclosure to the user(s) could impede an investigaion or obstruct justice.
The long answer
The longer answer considers what information you send to Signal. Because in theory, anything that you send them is something that they can possibly disclose.
The skeptic in me says that they can provide more information if it is requested in a different manner. As an example, look at what ProtonMail had to provide law enforcement as a result of a court order. They were compelled to log the IP address(es) from which a specific user connected. They do not keep any IP address logs by normally.
I’m looking at this from the perspective of someone that could tap into the stream of data being sent through Signal’s infrastructure. With that in mind, here are a few things that are sent to Signal that could potentially be revealed:
- your IP address
- to/from of message
- general message size - enough that someone could generally identify whether a text, picture, or video is being sent.
- timestamp of message send/receive/open
- contact list
I have not done an in depth analysis of Signal’s message encryption, but am relying on code audits that have been performed by those with more experience and presume that the message content is entirely protected from sender to recipient.
Generally speaking, Signal isn’t a zero-trust system, it’s a trust Signal system. We have to trust that Signal is treating our data like they say because we have no other choice if we use Signal. I’ve mentioned in the past that I do have some concerns about Signal, but they are not yet big enough for me to want to abandon the platform.
The even longer answer
The even longer answer takes you down a rabbit hole that doesn’t fit most people’s threat model. Let me know if you’re interested in going down that rabbit hole, let me know and I might write another post with my theories.